If your business accepts card payments, PCI DSS isn’t just another compliance acronym — it’s something you need to understand early and implement correctly.
Many startups and fintech companies only realize this when a bank, payment gateway, or partner asks for PCI documentation. By then, fixing architecture mistakes becomes expensive and time-consuming.
Let’s break it down in simple, practical terms.
What Is PCI DSS?
PCI DSS stands for Payment Card Industry Data Security Standard. It is governed by the PCI Security Standards Council. PCI DSS applies to any organization that stores, processes, or transmits cardholder data.
This includes:
- E-commerce businesses
- Payment gateways
- Fintech startups
- SaaS platforms handling recurring payments
- Retail merchants
- Banks and payment aggregators
If you are working with Visa, Mastercard, RuPay, NPCI partners, or any acquiring bank, PCI DSS compliance is not optional.
What Is a PCI DSS SAQ?
Not every business needs a full audit by a Qualified Security Assessor (QSA). If you’re eligible, you can validate compliance by completing a Self-Assessment Questionnaire (SAQ) instead.
An SAQ allows you to:
- Complete the applicable SAQ form
- Provide evidence of required security controls
- Submit an Attestation of Compliance (AOC)
- Share documentation with your bank or payment partner
However, not all businesses qualify for the same SAQ. The SAQ you must complete depends entirely on how your systems handle card data.
Types of PCI DSS SAQs Explained (With Real Examples)
Let’s understand each SAQ type in plain language.
1. SAQ A – Fully Outsourced E-Commerce
When It Applies
When it applies:
You completely outsource payment processing to a PCI DSS validated provider.
Example:
A SaaS startup in Chennai:
- User signs up
- Clicks “Subscribe”
- Gets redirected to Razorpay or Stripe hosted checkout
- Payment happens entirely on the gateway’s page
- Confirmation comes back to the SaaS platform
Your systems:
- Do NOT store card data
- Do NOT process card data
- Do NOT transmit card data
✔ SAQ A applies.
Why this is ideal:
You drastically reduce your PCI scope. For most startups, this is the safest and smartest architecture decision.
2. SAQ A-EP – E-Commerce with Payment Page Integration
When it applies:
Your website hosts the checkout page, but payment processing is done by a third party.
Example:
A Mumbai-based D2C brand:
- Checkout page is hosted on their server
- Payment fields load via JavaScript from the gateway
- Card entry happens within their website layout
Even though the gateway processes the payment, your:
- Web server
- Application server
- Cloud environment
are now in scope. If your website gets hacked, attackers could inject malicious scripts.
✔ SAQ A-EP applies.
It’s significantly more complex than SAQ A.
3. SAQ B – Standalone Dial-Out Terminals
When it applies:
You use standalone dial-up card machines (no internet).
Example:
A small jewellery store in Coimbatore using a phone-line swipe machine.
✔ SAQ B applies.
Rare today, but still found in smaller towns.
4. SAQ B-IP – Internet-Based Card Terminals
When it applies:
IP-connected POS terminals.
Example:
A restaurant chain in Hyderabad:
- POS machines connected via broadband
- No card data storage
- Proper network segregation
✔ SAQ B-IP applies.
Here, network segmentation becomes critical.
5. SAQ C – Payment Application Connected to InternetWhen it applies:
You use payment software connected to the internet but do not store card data.
Example:
A retail chain using internet-enabled POS software without storing PAN.
✔ SAQ C applies.
6. SAQ C-VT – Virtual Terminal
When it applies:
Manual card entry via web portal.
Example:
A travel agency in Delhi:
- Customer shares card details over phone
- Staff enters details into gateway portal
- Dedicated system used
- No storage
✔ SAQ C-VT applies.
7. SAQ P2PE – Validated Point-to-Point Encryption
When it applies:
You use PCI SSC validated encrypted terminals.
Card data is:
- Encrypted immediately at swipe
- Impossible for merchant to decrypt
✔ SAQ P2PE applies.
This significantly reduces scope.
8. SAQ D – The Most Comprehensive SAQ
If you:
- Store cardholder data
- Build your own payment engine
- Process transactions internally
- Develop fintech infrastructure
You likely fall under SAQ D.
Example:
A fintech applying for NPCI ecosystem integration:
- Stores encrypted tokens
- Runs API infrastructure
- Operates cloud payment layer
✔ SAQ D is mandatory.
This includes nearly all PCI DSS requirements.
How Indian Fintechs Should Plan Infrastructure Before PCI DSS?
Most businesses make the same mistake: They build first. They think about compliance later.
That approach leads to:
- Expensive re-architecture
- Failed audits
- NPCI onboarding delays
- Increased VAPT findings
Here’s how to plan correctly.
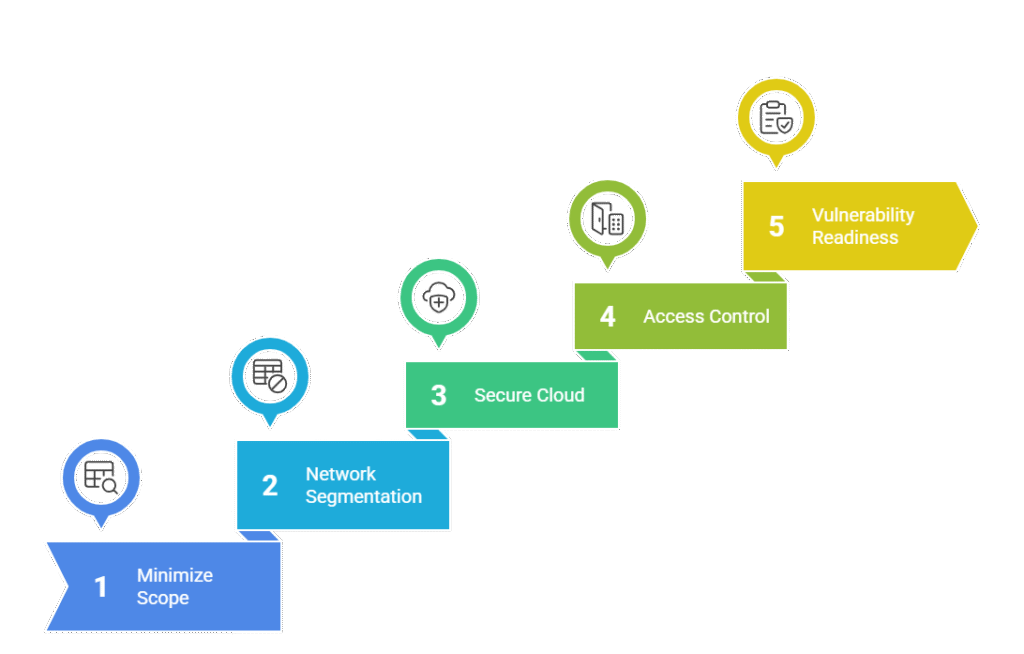
Step 1: Minimize Your PCI Scope
Golden rule:
If you don’t touch card data, you reduce 60% of compliance burden.
For startups:
- Use hosted checkout.
- Avoid storing PAN.
- Use tokenization.
This is highly recommended for early-stage fintechs.
Step 2: Network Segmentation
If you must handle card data:
- Separate Cardholder Data Environment (CDE)
- Implement firewall rules
- Block unnecessary traffic
- No shared corporate WiFi
Many Indian audits fail here.
Step 3: Secure Cloud Architecture
For AWS/Azure/GCP deployments:
- Harden VMs
- Enable encryption at rest
- Use MFA for admin access
- Deploy WAF
- Enable centralized logging
PCI DSS v4.0 emphasizes continuous monitoring.
Step 4: Access Control & Monitoring
- Role-based access
- No shared accounts
- MFA for administrators
- Log monitoring
- Incident response planning
These are critical for NPCI review.
Step 5: Vulnerability & VAPT Readiness
Before PCI submission:
- Conduct CERT-In empanelled VAPT
- Fix high & critical findings
- Perform ASV scanning
- Maintain patch management evidence
Indian regulators are strict about VAPT compliance.

PCI DSS & NPCI Context
If you are working with NPCI or applying for:
- Payment aggregator license
- Issuer partnership
- Switching network integration
You may need:
- PCI DSS
- ISO 27001
- CERT-In VAPT
- Secure architecture documentation
NPCI expects strong security posture. Even if SAQ applies, documentation and evidence are critical.
Quick SAQ Comparison
| SAQ Type | Business Type | Card Storage | Complexity |
| SAQ A | Fully outsourced e-commerce | No | Low |
| SAQ A-EP | Integrated e-commerce | No | Medium |
| SAQ B | Dial-out terminals | No | Low |
| SAQ B-IP | IP terminals | No | Medium |
| SAQ C | Internet-connected app | No | Medium |
| SAQ C-VT | Virtual terminal | No | Low |
| SAQ P2PE | Encrypted terminals | No | Low |
| SAQ D | All others | Yes / Complex | High |

Common Mistakes Indian Businesses Make
❌ Choosing SAQ A when A-EP applies
❌ Storing card data temporarily in CRM
❌ Mixing PCI systems with office laptops
❌ No documented incident response
❌ Ignoring log review
These lead to compliance rejection.
Why Planning Early Saves Cost
Proper PCI-aligned architecture:
- Reduces audit effort by 40–60%
- Speeds up bank approvals
- Improves investor confidence
- Minimizes breach risk
Compliance should not be an afterthought. It should be part of product design.
Final Thoughts
Choosing the correct PCI DSS SAQ type is not just a documentation exercise. It reflects how securely your infrastructure is designed.
If you are unsure:
- Conduct a PCI scope assessment
- Map data flow diagrams
- Review network segmentation
- Evaluate storage practices
Making the right decision early can save months of delay.
PCI DSS Consulting for Indian Fintech & SaaS
If your organization is:
- Preparing for NPCI onboarding
- Applying for Payment Aggregator approval
- Launching a fintech platform
- Handling cardholder data
- Unsure which SAQ applies
We can help with:
✔ PCI Scope Assessment
✔ SAQ Selection Guidance
✔ Gap Assessment & Remediation
✔ Network Architecture Review
✔ Documentation & Policy Preparation
✔ ASV & VAPT Coordination
✔ End-to-End PCI DSS Implementation Support
We specialize in helping Indian fintechs and SaaS companies achieve PCI DSS compliance in a practical and cost-efficient way.
📩 Contact us today for a PCI readiness assessment.
Frequently Asked Questions (FAQs) – PCI DSS SAQ & Compliance in India
A PCI DSS Self-Assessment Questionnaire (SAQ) is a validation document used by eligible merchants to confirm compliance with PCI DSS requirements without undergoing a full audit by a Qualified Security Assessor (QSA).
The type of SAQ depends on how your organization stores, processes, or transmits cardholder data.
The applicable SAQ depends entirely on your payment architecture:
– Fully outsourced payment page → SAQ A
– Hosted checkout page integrated with gateway → SAQ A-EP
– Standalone card terminals → SAQ B or B-IP
– Manual web-based entry (Virtual Terminal) → SAQ C-VT
– Card data storage or complex infrastructure → SAQ D
If you store cardholder data, you almost always fall under SAQ D.
Yes. Any organization in India that accepts, processes, or transmits cardholder data must comply with PCI DSS. This is required by:
– Acquiring banks
– Payment networks (Visa, Mastercard, RuPay)
– Payment aggregators
– Regulatory expectations tied to NPCI ecosystem
Even startups and SaaS companies are not exempt.
While NPCI does not directly certify PCI DSS, organizations integrating with NPCI ecosystem (issuers, aggregators, fintech platforms) are typically required by banks and payment partners to demonstrate PCI DSS compliance.
In most fintech onboarding cases, PCI DSS becomes a mandatory prerequisite along with:
– ISO 27001
– CERT-In VAPT
– Secure architecture documentation
This is one of the most misunderstood areas in PCI DSS compliance.
SAQ A applies when:
– You completely redirect customers to a PCI-compliant payment provider.
– Your servers never host payment fields.
SAQ A-EP applies when:
– Your website hosts the checkout page.
– Payment fields load via script or iFrame.
– Your infrastructure can influence payment security.
If your website can be hacked to inject malicious code, SAQ A-EP likely applies.
SAQ D is the most comprehensive Self-Assessment Questionnaire.
It applies when:
– You store cardholder data.
– You process payments internally.
– You operate complex payment infrastructure.
– You do not qualify for simpler SAQs.
SAQ D includes nearly all PCI DSS requirements, including:
– Network security controls
– Vulnerability management
– Logging & monitoring
– Access control
– Incident response
– Secure development practices
Most fintech companies fall under SAQ D.
No. However, start-ups can significantly reduce PCI DSS scope by:
– Using hosted checkout solutions
– Avoiding storage of card data
– Implementing tokenization
– Minimizing system interaction with PAN
Architectural decisions at early stage determine compliance complexity later.
PCI DSS validation is typically done annually. However, compliance is continuous.
You must:
– Perform quarterly vulnerability scans (if applicable)
– Conduct annual penetration testing
– Maintain continuous logging & monitoring
– Review access regularly
PCI DSS v4.0 emphasizes ongoing security rather than annual checkbox compliance.
Choosing the wrong SAQ can result in:
– Bank rejection
– Compliance failure
– Regulatory scrutiny
– Delayed NPCI onboarding
– Increased remediation costs
A PCI DSS scope assessment should always be conducted before selecting the SAQ type.
If your business only handles UPI and does not process cardholder data, PCI DSS may not apply.
However, if you accept debit or credit cards in any capacity — even through third-party processors — PCI DSS compliance is required.
Many Indian fintech platforms handle both UPI and cards, making PCI DSS applicable.
It depends on:
– Merchant level (transaction volume)
– Bank requirement
– Regulatory expectation
– Business model
– Incident history
Large merchants and service providers may require a full QSA audit instead of SAQ.
Typical timelines:
– Small SAQ A merchant: 4–6 weeks
– Mid-size SaaS / e-commerce: 8–12 weeks
– Fintech under SAQ D: 3–6 months (depending on architecture readiness)
If infrastructure is not designed securely, timelines increase significantly.
Before starting PCI DSS compliance, you should:
– Perform PCI scope assessment
– Create network and data flow diagrams
– Implement segmentation
– Enable centralized logging
– Conduct vulnerability assessment
– Harden cloud infrastructure
– Document policies and procedures
Compliance planning must begin before infrastructure scaling.
Yes. PCI DSS v4.0 introduces:
– Stronger authentication controls
– Increased logging requirements
– Risk-based approaches
– Enhanced security testing
– Greater emphasis on continuous monitoring
Even SAQ-based environments must now demonstrate stronger security maturity.
Typical documentation includes:
– Information Security Policy
– Access Control Policy
– Incident Response Plan
– Risk Assessment
– Network Diagram
– Data Flow Diagram
– Vulnerability Scan Reports
– Attestation of Compliance (AOC)
Proper documentation is critical for bank acceptance.