Meeting SOC 2 compliance can be daunting for startups with fewer than 50 employees. Security compliance is often neglected as a secondary priority because of limited resources, a lean team, and rapid growth. Nevertheless, SOC 2 is not only a box game, but also a strong signal of trust to the customers, investors, and partners. In the modern world of competition, even companies in the initial stages of development are anticipated to have good data protection and internal controls. It is all about knowing what is really important. Under the correct approach, SOC 2 is controllable, economical, and scalable, aiding startups to establish credibility without losing agility and innovativeness.
Why does SOC 2 compliance matter for startups with 50 employees?
SOC 2 compliance is very important at the business level as the stakes are high. Even one security breach can destroy years of reputation, customer affairs, and even multimillion-dollar dealings. Companies that do business with large businesses are under increased review, and clients and regulators are seeking watertight evidence of security before the contracts are added.
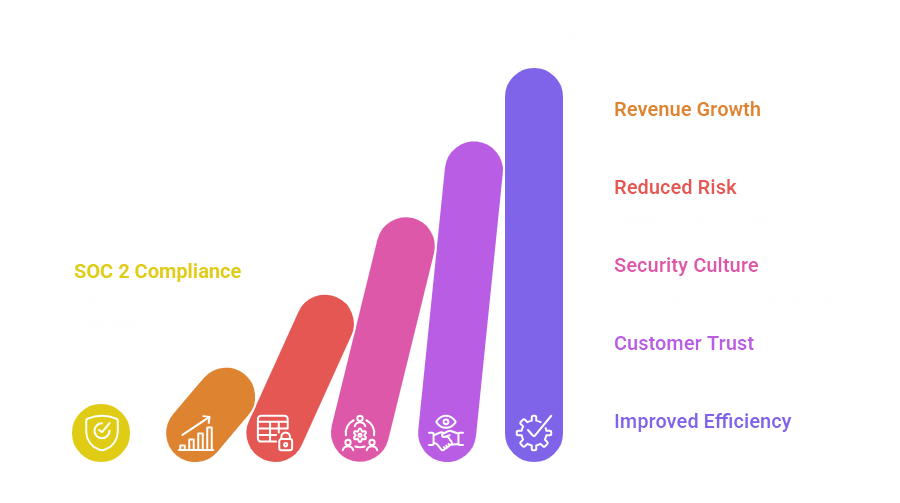
Scales and Expedites Revenue Growth
Companies that offer their products to mid-market or enterprise buyers soon find that security audits play a role in any sales process. A SOC 2 report is regularly requested by procurement teams when they sign the contracts. Without it, deals may stall or worse, they may vanish.
In the case of a 50-employee startup, SOC 2 is a source of revenue accelerator. Your audited controls can give the standardized evidence of security practices, and you do not have to fill in lengthy security questionnaires time and again.
It also introduces wider customers. A good number of businesses would not even think of using vendors who are not even SOC 2 compliant. Through early investment, startups are positioned to compete in larger markets and secure valuable contracts.
Reduces the Risk of Significant Cybersecurity Gaps
Startups grow more complex as time goes by, adding many SaaS providers, cloud solutions, third parties, and remote teams. Security holes may develop easily in the absence of formalized controls.
SOC 2 expects organizations to analyze risks in the areas of security, availability, processing integrity, confidentiality, and privacy. This is a systematic risk management process that assists in pinpointing areas of weakness before hackers. Be it the misuse of access controls, the use of weak password policies, or a lack of monitoring, compliance mandates compel startups to correct weaknesses beforehand.
A single data breach can be devastating to a 50-person company in terms of financial and reputational damage. Legal expenses, customer leakage, and investor confidence are factors that can badly interfere with expansion. SOC 2 offers a framework that substantially reduces the chances of this kind of incident as it entrenches preventive and detective controls in everyday operations.
Helps Establish a Security-First Culture
Startups are organized around speed and innovation; however, the absence of discipline may lead to chaotic operations. SOC 2 brings about governance, accountability, and documented procedures. It makes sure that the security burdens are well spelled out, formalizes the policies, and ensures that the employees are aware of their part in data protection.
By adhering to well-defined onboarding, access control procedures, and incident response guidelines and policies, security turns into the company’s DNA, as opposed to merely the duty of the IT team. Awareness of phishing, social engineering, and data management best practices is also created through training requirements.
The application of SOC 2 aids in instilling a security-first culture into the organization at an early phase, and hence, compliance will be easy to uphold as the company grows.
Gains Customer Trust and Confidence
The competitive differentiator is trust. Customers would like to know that their data is safe, particularly in case the startup manages sensitive data such as financial, healthcare, or personal data.
A SOC 2 report proves that your internal controls are assessed and confirmed by an independent auditor. This third-party checking generates credibility that is way better than marketing statements. It also gives customers confidence that your startup is up to the accepted industry standards in terms of security and operational integrity.
Where there are young companies against other companies that are larger and established, the SOC 2 level the playing field. It offers concrete evidence that you have advanced security practices despite your size.
Improves Internal Processes and Efficiency
As much as some founders see SOC 2 as a burden in terms of compliance, it tends to provide benefits in operations. It involves the documentation of workflows, responsibilities, and standards of processes.
This transparency eliminates misunderstandings and a lack of efficiency. Privileged assignment becomes simplified. Response incidents are more synchronized and quicker. Vendor management is now organized and not haphazard. Monitoring and internal audit help in improvement.
In the case of a startup that has 50 employees, job descriptions can be similar, and procedures can be developed rapidly; SOC 2 brings some sanity without losing the flexibility. It presents disciplined mechanisms that help in sustainable development.
What steps do startups follow to be SOC 2 compliant?
For startups, SOC 2 compliance may initially seem complicated, but when broken into simple steps, it can be managed and planned. The following are the key steps that most startups undergo to attain compliance with success.
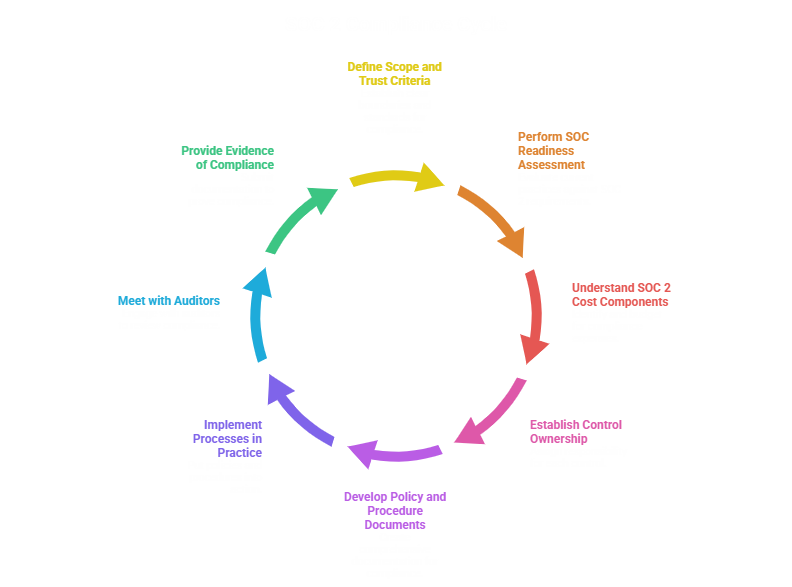
Defining Scope and Trust Criteria
The initial step is to establish what systems, services, and data are within the SOC 2 boundary. When it comes to startups, it is necessary to identify which products, infrastructure elements, and internal operations will be audited. Attempts to incorporate everything may complicate and render compliance unnecessary and expensive.
Secondly, startups choose the relevant Trust Services Criteria, which include Security (which must be used), and optionally Availability, Processing Integrity, Confidentiality, and Privacy. Security principle is usually the starting point of the SaaS startup, and then it is developed further as the needs of customers increase. Scoping helps to be focused, minimizes the complexity of the audit, and ensures that compliance is directed at the actual risk to the business.
Performing a SOC Readiness Assessment
Startups have a readiness assessment (alternatively known as a gap assessment) before they engage auditors. This step examines existing controls and compares them to SOC 2 requirements and finds areas of weakness.
The evaluation examines policies, access controls, change management processes, vendor management practices, and monitoring processes. This is to find out what is lacking and what should be remedied before the actual audit.
Understanding SOC 2 Cost Components
SOC 2 expenses are different in relation to scope, the kinds of audit (Type I and Type II), company size, and the complexity of the infrastructure. Early knowledge of the cost drivers will assist startups in planning realistically. In companies with approximately 50 workers, expenses are usually lower than those of larger enterprises, particularly when systems are already cloud-native and well-structured. There are a number of elements that should be budgeted by startups:
- Audit firm fees
- Tools of compliance automation (in case)
- Internal resource time
- Legal/consulting assistance (where necessary)
- Improvement of security tooling.
Establishing Control Ownership
The oft-referenced startup error is thinking that compliance is a solely IT process. SOC 2 engages in cross-functionality. Accountability definition will also guarantee that controls are not bypassed. Audit evidence is also a lot easier to glean when clear ownership is involved. Every control should have a clear owner who will be in charge of implementation and monitoring.
For example:
- Background checks and onboarding are the responsibilities of HR
- Change management and secure development belong to engineering
- IT has access control and system monitoring
- Risk management and governance are the property of leadership

Developing Policy and Procedure Documents
SOC 2 compliance revolves around documentation. They must be based on real-life practices, not some generic templates found on the internet. Auditors ensure that policies are operational as well as documented. Clear policies well written bring about standardization and a guideline on how compliance will continue.
Startups should develop official policies and procedures that would address such aspects as:
- Information security
- Access management
- Incident response
- Vendor management
- Business continuity
- Risk assessment
- Data classification
Implementing the Processes in Practice
It is not sufficient to have documented policies. They have to be operationalized by startups. This implies implementing access controls, employee security training, periodical access reviews, system activity logs, formal code change management, and routine risk assessment.
In the case of a Type II audit, controls should work steadily during the time of observation (usually 3-12 months). This involves discipline and constant supervision. In most cases, automation tools assist startups in managing evidence, configurations, and simplifying compliance processes.
Meeting with the Auditors
After controls have been implemented and are running, startups seek the services of a CPA firm to audit them. Planning meetings form the starting point of the audit as the scope, systems, and timelines are affirmed.
Auditors analyze paperwork, conduct interviews with control owners, and review configurations of systems. In Type II audits, they examine the functioning of controls in the course of observation.
Providing Evidence of Compliance
Evidence is crucial to SOC 2. Startups have to demonstrate the presence of controls that are effective. Evidence should be coherent and dated and should be in line with the period of the audit. Well-developed evidence gathering is a sign of maturity and the high chances of a clean report.
This may include:
- Access review logs
- Change management tickets
- Security training records
- Test results of the incident response
- Vendor review documents
- Risk assessment reports

Conclusion
To sum it up, compliance with SOC 2 means not only passing an audit but also creating a secure, scalable, and trustworthy organization. In start-ups, particularly those employing approximately 50 people, the process deepens internal controls, increases operational discipline, shortens sales cycles, and instills customer trust. Startups can transform SOC 2 into a strategic opportunity and not a liability by tackling compliance in stages, i.e., defining scope, assigning ownership, implementing controls, and ensuring evidence-keeping. In case you are looking to have a startup-friendly process, Matayo provides SOC 2 preparedness, implementation, and audit support, allowing you to grow your business and still be in compliance.

