Managing credit card information entails a great deal of responsibility. Organizations that accept, transmit, or store cardholder information are required to comply with the Payment Card Industry Data Security Standard (PCI DSS). In order to safeguard payment data and lower fraud throughout the payment ecosystem, PCI DSS, an international framework, was developed. The PCI Security Standards Council created the standard to guarantee that companies handling card data maintain robust security controls.
For service providers such as payment gateways, cloud service providers, SaaS companies handling payment data, and managed service providers, the compliance journey can feel overwhelming even before the official assessment begins. In order to support secure payment processing, organizations must map their systems, comprehend the requirements, and set up the infrastructure. This blog provides a practical step for organizations before the pre-implementation stage of PCI DSS compliance.
Understanding PCI DSS for Service Providers
Sensitive data, such as the Primary Account Number (PAN), card verification codes, and other authentication information, is carried with every payment transaction. These data components could be used for fraud or identity theft if they are made public.
In order for organizations to safeguard this data throughout its lifecycle, PCI DSS creates a uniform security framework. It outlines a set of security guidelines that businesses must adhere to in order to safeguard stored card information, monitor access, secure payment networks, and uphold robust security governance. The framework is applicable to all organizations that process payments, such as financial institutions, payment gateways, technology service providers, and retailers.
PCI compliance, a complex and technical process, begins well before audits and security controls. This much challenging and strenuous process starts with steps that involve defining scope, mapping cardholders’ data flows, assessing existing security and regulation practices and documentation policies.
As PCI DSS introduced additional expectations like stronger authentication requirements and enhanced monitoring for security roles, organizations often feel that this process is a herculean task. But if we start early with strong groundwork, this is attainable.
Pre-Implementation Steps for PCI DSS Security Control
Before beginning with the implementation process, organizations have to go through an important preparatory stage involving ten core security requirements. It is designed to safeguard cardholders’ data and protect the payment environment. The knowledge of these ten stages helps organizations prepare their infrastructure before the formal implementation stage.
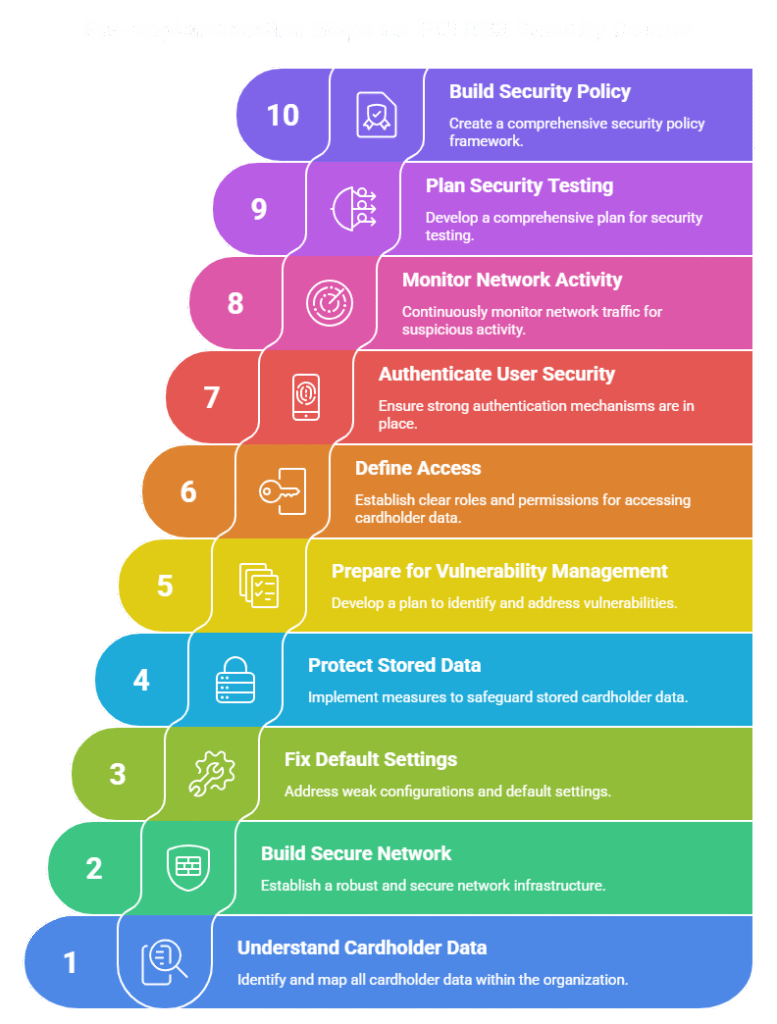
Step 1: Understanding Cardholder Data Environment
Finding the Cardholder Data Environment (CDE) is the first step. This covers all programs, systems, and network elements that handle or store credit card data. Businesses need to decide where card information enters their systems, how it travels between apps, and where it is kept. Determining the extent of PCI DSS compliance is aided by mapping these data flows. Businesses run the risk of overlooking systems that require security if the CDE is not clearly visible.
Step 2: Build a Secure Network
It is important to isolate the payment network from other corporate networks to protect the cardholder data environment. For this, two things should be done. Installation of firewalls and routers. The firewall deploys restrictive rules to regulate network traffic. To avoid vendor defaults, the company should apply secure configurations to all system components. To comply with PCI, organizations must create an inventory of all devices affecting the cardholder environment. They need to ensure that every cardholder has secured password and appropriate security settings.
Step 3: Fix Default Settings and Weak Configurations
Systems are frequently deployed with factory passwords or default configurations, which leads to security incidents. These well-known settings are frequently used by attackers to obtain unauthorized access.
Organizations must use secure configuration standards for all devices linked to the payment infrastructure and remove default credentials in accordance with PCI DSS. Servers, databases, network equipment, and payment apps fall under this category.
Organizations usually set configuration baselines that specify safe operating system, database, and application settings during implementation. Systems are consistently hardened against common vulnerabilities thanks to these baselines.
Step 4: Protect Stored Card Data
To maintain the data flow of cardholders, encryption should be used with a strong algorithm, and secure encryption keys should be employed to render data unreadable to unauthorized users. Organizations must use data discovery tools that scan data sources for primary account numbers (PAN) can help identify sensitive credit card details.
Cardholder data must be encrypted while in transit as well. Therefore, Publicly Available Networks require Advanced Encryption, with strict adherence to protocols such as (SSH) and (TLS) when transmitting Cardholder Data over an open network, such as via Bluetooth, the GSM or GPRS Mobile Phone Networks, or the Internet.
Step 5: Prepare for Vulnerability Management
For Organizations to keep their systems secure, continuous Monitoring for Malware and vulnerabilities must follow. As determined by PCI DSS Requirement, Anti-Malware Software and appropriate System Security Updates & Patches shall be made available to Organizations subject to PCI DSS Compliance.
The tools and techniques that organizations utilize during this phase of compliance include endpoint protection software (EPS), automated patch management systems (APMS), and vulnerability scanning tools (VST). These tools help organizations detect malware and prevent hackers from exploiting unpatched vulnerabilities. Consequently, systems that undergo regular review and updates to their defenses are less likely to be affected by the ever-evolving landscape of cyberthreats.
Step 6: Define Who Gets Access
To safeguard cardholder data against access by unauthorized individuals, the access to where this data will be stored must be tightly managed. Major companies should restrict access to cardholder data and data storage items so that employees who do not work with this data do not have access to it. Employees with access to cardholder data should only have access to the data based on the job they perform, and the specific duties assigned to them for that position, regardless of how securely the data may be stored. The measures like role-based access control (RBAC) and robust authentication mechanisms should be approached.
Step 7: Authenticate User Security
All people granted access to cardholder data must possess their own unique identifiers (ID), such as an employee ID or username. Two-factor authentication (2FA) is also required for all individuals granted access to cardholder data; for example, to gain access, employees must present both a physical item (such as a security token) and a password to prove their identity. The highly secure RADIUS or TACACS tokens are advised by the PCI standard.
Step 8: Monitor Network Activity
Continuous monitoring of the integrity of stored cardholder data requires that organizations monitor all access to the cardholder data and all network resources safeguarded by the cardholder data, to comply with PCI DSS. Logging systems capture system activities and events, including user access, administrative tasks, and security event occurrences on a particular system. To support intrusion detection, logging systems must safeguard and review logs frequently. Many companies have consolidated their security operations and the analysis of security events across the organization by utilizing centralized logging systems or security information and event management systems.
Step 9: Plan Security Testing
Regularly scheduled penetration testing of your network and systems is necessary in order to determine if there are any vulnerabilities present. In addition to performing regular penetration testing, organizations must perform vulnerability scans of their systems, networks, and applications, such as intrusion detection and prevention systems (IDS/IPS), to find and remediate vulnerabilities. All security testing should be conducted by qualified individuals using tools and procedures that have been approved by their organization.
Step 10: Build Your Security Policy Framework
Well-documented security policy is the key requirement for the implementation stage. Organization also needs to duly frame internal security policies, procedures, and processes in compliance with PCI DSS. Support information security with organizational policies and programs. This is a long but sustainable process of documenting each step involving maintaining an inventory of hardware and software assets, framing policies of access control, regulated encryption practices, incident response procedures, and employee training programs. The documented policies should be reviewed annually based on a formal risk assessment, and employees and others with access to the cardholder environment must undergo training.
Turning Compliance into Long-Term Security
After the preparation is completed, organizations may proceed with the Self-Assessment Questionnaire (SAQ) or a formal audit, depending on their transaction volume and service provider status. The SAQ is a structured questionnaire that aims to evaluate whether an organization meets PCI DSS requirements. It is important to remember that achieving PCI DSS compliance is not just a one-time event. There are many ways for attackers to exploit vulnerabilities, and the payments landscape continues to change. For this reason, organizations must execute continuous policy updates, perform frequent security testing, and conduct ongoing monitoring.

Conclusion
By properly managing the preparatory stages of compliance, the complex process of achieving PCI DSS compliance can become manageable, ongoing and benefit both consumers and organizations alike. Need help achieving PCI DSS compliance? Matayo offers expert support from gap assessment to certification and continuous compliance management. Contact their team to simplify your PCI DSS journey and secure your payment infrastructure.

