A careless privacy step can turn a routine business day into a legal storm. Under the DPDPA, some mistakes stay quiet until a notice, breach, or complaint arises. You may think consent banners and policies cover enough, yet small gaps bring sharp risk. A weak notice, slow reply, loose access control, or poor complaint path can hurt fast. One missed check can drag your brand into trouble. The price is not only money; trust falls, teams scramble, and customers remember the mess. You should fear hidden compliance mistakes more than the loud, obvious ones. You need clean records, clear words, safe systems, and real answers when people ask. You will see where businesses slip, even when daily work looks normal and harmless. Fix these blind spots early, or ₹250 crore can stop feeling like a distant headline.
Understanding the DPDPA Act and Its Importance in Business
The DPDPA is not a soft privacy guideline or a branding exercise. It is a statutory compliance framework for digital personal data processing. If your business determines why personal data is collected and how it is used, you operate as a Data Fiduciary. If a vendor processes that data on your behalf, that vendor functions as a Data Processor. The law applies to digital personal data collected in India, and it also reaches processing outside India when your business offers goods or services to people in India. That widens the compliance perimeter fast.

Your website forms, onboarding stack, CRM, ticketing tools, payment systems, ad-tech integrations, analytics layer, cloud storage, and internal HR platforms all fall into scope when they process personal data. Also, the Act is built around defined control points: lawful purpose, valid consent, notice architecture, rights enablement, breach response, retention discipline, and reasonable security safeguards. So privacy is no longer just a policy page. It becomes an operating model with governance, auditability, and accountability built into daily business systems.
What is the Maximum Penalty a Company Can Face Under DPDPA?
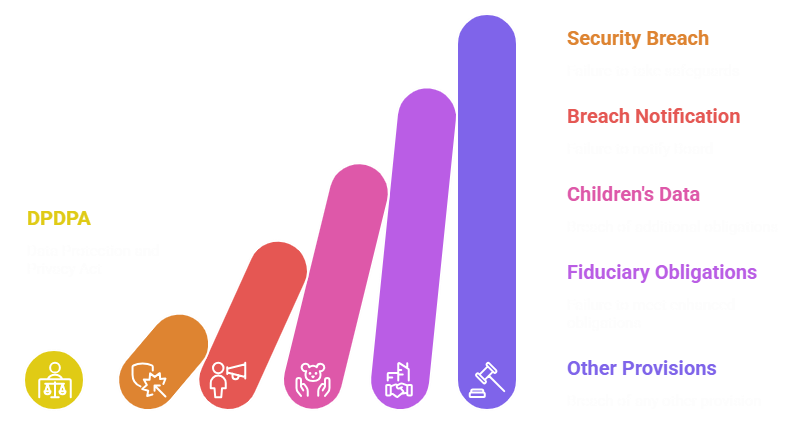
The maximum monetary penalty under the DPDPA can reach ₹250 crore, and that top exposure is tied to failure to take reasonable security safeguards to prevent a personal data breach. That single number changes the stakes for every company handling personal data at scale. The Schedule also sets other major penalty bands. Failure to notify the Board and each affected Data Principal of a personal data breach can attract up to ₹200 crore. Breach of the additional obligations relating to children can also go up to ₹200 crore. If your business is classified as a Significant Data Fiduciary, and you fail to meet the enhanced obligations under section 10, the penalty can rise to ₹150 crore. For breach of any other provision of the Act or the rules, the monetary penalty can extend to ₹50 crore. In plain terms, the risk is not limited to one catastrophic cyber incident. It also sits in weak internal controls, delayed escalation, poor breach notification workflows, defective consent handling, or missing governance around high-risk processing. However, the ₹250 crore figure remains the sharpest signal: technical safeguards are not optional hygiene. Under this law, they are a core legal obligation.
How Does the DPDP Act Decide Penalty Amounts?
The DPDPA does not use a flat-rate penalty model. The Board has to evaluate the breach context before imposing a monetary penalty. First, it looks at the nature, gravity, and duration of the breach. Second, it considers the type and nature of personal data affected. Third, it checks whether the breach is repetitive, which is critical because repeated failures suggest control weakness, not a one-off lapse. The Board also examines whether the person or business realized a gain or avoided a loss because of the breach. This matters where shortcuts deliver speed, scale, or cost savings. In addition, the Board considers whether timely and effective mitigation steps were taken after the incident.
5 Hidden DPDPA Compliance Mistakes That Can Cost Your Business ₹250 Crore
The most expensive compliance failures hide inside your data lifecycle, your product defaults, your vendor workflows, and your incident-response blind spots until one complaint, one breach, or one audit makes everything visible.
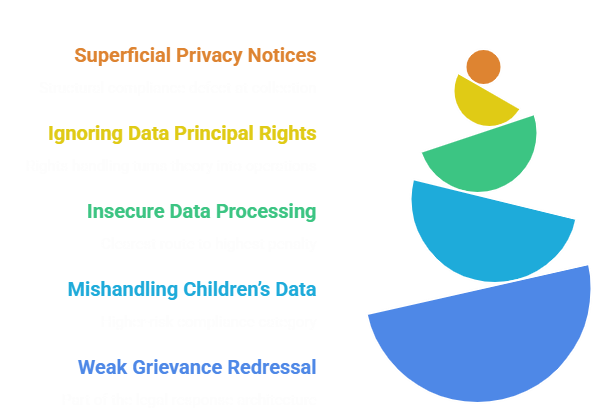
Superficial Privacy Notices
A superficial privacy notice creates a structural compliance defect right at the point of collection. Under the Act, a consent request must be accompanied or preceded by a notice that informs the Data Principal about the personal data being processed, the purpose of processing, how rights may be exercised, and how a complaint may be made. Consent itself must be free, specific, informed, unconditional, unambiguous, and backed by clear affirmative action. That is a tight legal standard, and many businesses miss it in very technical ways. For example, purpose statements are often too abstract, bundled, or elastic. A notice says data is processed to “improve services,” but it does not separate KYC, fraud screening, analytics, marketing, profiling, or third-party enrichment. That creates purpose opacity. Also, many interfaces still use dark-pattern style design, where the consent UX is easy, but withdrawal or refusal is buried. That weakens consent validity.
Ignoring Data Principal Rights
Rights handling is where privacy compliance turns from theory into operations. The Act gives the Data Principal a right to access information about personal data, seek correction, completion, updating, and erasure, and use a grievance redressal mechanism. Where consent is the basis of processing, the Data Principal can also withdraw consent at any time, and the law says the ease of withdrawal should be comparable to the ease with which consent was given. That single phrase has serious technical implications. Your systems must support rights orchestration across apps, databases, archives, and third-party processors. However, many businesses still handle rights manually through email chains, shared spreadsheets, and fragmented ticket queues. That is risky. A deletion request may stall because no one knows where backup copies sit. A correction request may update the front-end profile but not the billing system or fraud database. A consent withdrawal may stop email marketing but leave analytics tags and audience syncs running. This is how non-compliance grows quietly. If your rights workflow lacks identity verification logic, SLA tracking, escalation rules, system-level propagation, and processor coordination, then the issue is not slow service. It is a control failure at the data governance layer.
Insecure Data Processing
Insecure data processing is the clearest route to the highest penalty band, and it often starts with ordinary technical debt. The Act requires a Data Fiduciary to protect personal data in its possession or under its control, including processing done by a Data Processor, by taking reasonable security safeguards to prevent personal data breaches. It also requires appropriate technical and organizational measures to ensure effective observance of the law. So the legal obligation is not limited to firewalls or encryption alone. It covers the full control stack: identity and access management, least-privilege provisioning, secrets handling, environment segregation, patching cadence, logging, monitoring, secure software development practices, vendor oversight, and breach containment readiness. A breach under the Act is also defined broadly. It includes unauthorized processing, accidental disclosure, acquisition, sharing, use, alteration, destruction, or loss of access that compromises confidentiality, integrity, or availability.
Mishandling Children’s Data
Children’s data sits in a higher-risk compliance category, and product teams often underestimate how strict that risk becomes. Under section 9, before processing the personal data of a child, the Data Fiduciary must obtain verifiable consent from the parent or lawful guardian. The Act also prohibits tracking, behavioral monitoring of children, and targeted advertising directed at children, subject to limited exceptions that may be prescribed. That means your age-gating controls, parental verification workflows, ad-tech integrations, recommendation systems, and behavioral analytics design need close review. For example, a gaming platform that profiles minors for engagement optimization, or an education app that deploys third-party trackers without robust age-aware controls, may create compliance exposure even when the product team sees the feature as standard growth tooling. Also, many organizations have no formal age-classification logic at intake, so users self-declare with no validation and move straight into normal data pipelines. That is not a safe control environment. If your business processes children’s data, you need policy, product, engineering, and ad operations aligned around verifiable consent, prohibited processing patterns, retention limits, and evidence trails. Otherwise, a seemingly small feature can escalate into a ₹200 crore risk surface.
Weak Grievance Redressal
Grievance redressal sounds administrative, but under the Act, it is part of the legal response architecture. A Data Principal has the right to have readily available means of grievance redressal provided by the Data Fiduciary or Consent Manager, and the grievance must be responded to within the prescribed period. For a Significant Data Fiduciary, the Data Protection Officer must be based in India, responsible to the Board of Directors or similar governing body, and serve as the point of contact for the grievance mechanism. That means grievance handling cannot be treated as a dead-end inbox or a customer support side task. It is a regulated workflow. However, this is where many organizations expose their weakest internal wiring. Complaints are not classified correctly. Rights requests are mis-tagged as generic support queries. Legal review happens too late. Product and security are never looped in. No escalation matrix exists. No closure logic is documented. No root-cause analysis follows repeat complaints. Well, that is not just bad service. It is evidence of weak privacy operations.

Conclusion
DPDPA risk grows quietly when small privacy gaps are ignored for too long. You may not see trouble early, but the damage builds fast. The biggest mistakes often hide inside normal tasks, forms, and systems. So, fix the quiet gaps now, before they turn into costly penalties. For practical DPDPA support, choose Matayo AI now.