May 2027 is closer than it looks, and your data duties are growing. If your business collects names, numbers, emails, or IDs, this matters. The DPDPA asks you to treat personal data with care, clarity, and purpose. That means knowing what you collect, why you keep it, and who sees it. You need clean notices, clear consent, safe systems, and simple records. You also need a plan for vendors, risks, complaints, and breaches. Small gaps can turn into legal trouble, lost trust, and messy fixes. A strong checklist helps you spot weak points before they become real problems. It brings order to your policies, teams, tools, and daily decisions. This guide shows the key steps Indian businesses should finish before May 2027. You will see what to review, what to fix, and what to document. The goal is simple: stay ready, stay careful, and earn lasting trust.
DPDPA Compliance Checklist for Indian Businesses
May 2027 is not the month to start fixing privacy gaps. It is the month by which your controls, records, workflows, and decision trails should already work in real life. The rules now follow a phased path, and the big operational lift sits in notice design, consent handling, rights response, security safeguards, breach reporting, and proof that your vendors do not weaken your posture. So this checklist is not about pretty policy files. It is about building a working privacy operating model that can survive audits, complaints, and messy day-to-day business pressure.
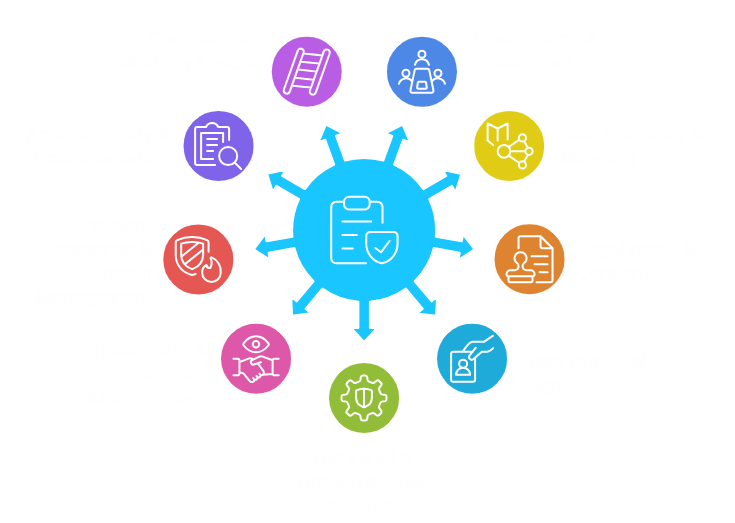
Governance & Leadership
Start with ownership, because vague ownership kills compliance fast. Every business needs one accountable privacy lead, a cross-functional steering group, and a board-facing risk view that gets reviewed on a schedule. If you are later classified as a Significant Data Fiduciary, the bar jumps higher: you need a Data Protection Officer based in India, an independent data auditor, periodic impact assessments, periodic audits, and stronger checks on systems that could affect people at scale. Even if you are not there yet, act like a serious operator now. Build a RACI matrix, a privacy risk register, a policy stack, and a change-control gate so new products, new campaigns, and new integrations do not go live without a data review. That one step, honestly, saves months later.
Data Inventory & Mapping
You cannot protect data that you have not found. Making it your first big task, then is a complete data inventory across applications, CRM applications, human resource applications, knowledge of your eyes, knowledge of your customer, knowledge of your support team, knowledge of your finance tools, knowledge of your marketing tools, knowledge of your cloud buckets, knowledge of your archives exports, scanned files, layer 1. The law covers digital personal data, such as that initially received in non-digital form and subsequently digitised, such as old paper forms scanned into shared drives, which still qualify. Assigned each dataset to purpose, source, system owner, internal users, external recipients, storage location, retention clock, and deletion trigger. Go deeper than surface systems. Include SDKs, analytics pixels, email platforms, outsourced call centers, payroll vendors, and data lakes that quietly copy fields from upstream systems. A practical map should show lineage end to end, not just where data rests.
Legal Basis & Consent
Under this framework, you should not pretend every processing activity runs on one giant checkbox. Each activity needs a lawful route, and for many business flows that means valid consent or another clearly permitted use under the Act. The consent should be free, specific, informed, unconditional, unambiguous, and linked with explicit affirmative action. It should also be restricted to data that is necessary at all within the said purpose. Your notice must be self-contained, in plain language, include the list of the data items, state the purpose clearly, and provide the direct links or paths to revoke consent, exercise rights, and complain. It implies a lack of bundling within long-term pages, hidden toggles, and dark patterns. Keep versioned notice text, consent timestamps, channel metadata, and proof of the exact user action. When challenged, the burden to prove notice and consent sits with the business.
Data Principal Rights
Inside your team, switch to the law’s own language and treat these as Data Principal rights. People can ask for a summary of data being processed, details of processing activities, and identities of other fiduciaries or processors with whom the data was shared, subject to narrow exceptions. They can seek correction, completion, updating, and erasure, unless some other law requires retention. They can raise grievances, and they can nominate another person to act if they die or become incapable. In addition, the rules expect rights channels to be prominently published on your website or app, and grievance systems should be built to respond within a period not exceeding ninety days. So do not run this off a random inbox. Build a real intake form, identity verification steps, ticket IDs, SLA clocks, escalation paths, and an audit trail for every response.
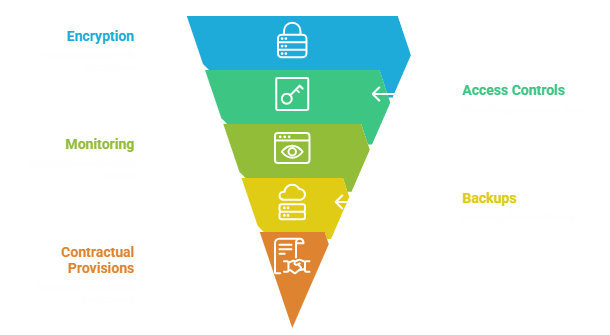
Technical & Organizational Measures
This is where many businesses get a bit lazy, and that is risky. The rules express a minimum level of security: encryption, obfuscation, masking, or virtual tokens; access controls to the computer resources that access personal data; logs, monitoring and review to detect unauthorized access; ability to back up continuity; contractual provisions to push the security to the processors; and technical and organizational measures to make the entire thing work. This means your checklist must cover important management, role/attribute-based access control, privileged access reviews, MFA on admins, database segmentation, secure backups, restore tests, DLP controls, and SIEM of key systems. Keep evidence too. A control that exists but leaves no trace is, well, hard to defend under pressure.
Third-Party & Vendor Management
Vendor risk is not a side issue here. A Data Fiduciary stays responsible even when processing is done on its behalf, and processors should be engaged only under a valid contract. That contract should do real work: define processing instructions, security controls, breach escalation, log retention duties, deletion and return rules, sub-processor conditions, audit rights, and support for rights requests and investigations. Review where each vendor stores, accesses, and replicates data. Check support tickets, sandbox copies, debug logs, offshore teams, and hidden subcontractors, not just the glossy security pack. Cross-border transfers need careful tracking because transfers outside India remain subject to restrictions the government may specify, and some Significant Data Fiduciaries may face tighter localisation measures for notified categories. In plain terms, every vendor touching personal data should be mapped, scored, contracted, and watched on a repeat cycle.
Incident Response & Breach Management
Your breach plan cannot live as a dusty PDF in some folder. It needs live roles, call trees, severity thresholds, forensic handoff steps, regulator messaging, and customer messaging that can move fast. The law provides breach notification to affected persons, and to the Board, and the rules supplement this. There is a need to be informed of affected persons immediately in plain and concise simple language, the nature of the breach, probable impacts, mitigation measures, advice on protection and contact information. This should be reported to the Board immediately, and the Board should be provided with a further detailed report within seventy-two hours unless further time is granted. Build templates now, run tabletop exercises, and preserve evidence. And ensure logs, snapshots and case notes are used to support root-cause analysis, since post-incident remediation is a compliance requirement, not a nice-to-have.
Accountability & Documentation
Documentation is where mature programs quietly win. You need a record system that can show what data you process, why you process it, what notice was shown, what consent was captured, when it was withdrawn, who approved the workflow, which vendor touched the data, what retention rule applied, and what happened during any incident or rights request. Keep Records of Processing Activities, notice versions, consent receipts, processor contracts, DPIAs, training logs, deletion logs, access review results, and committee minutes in one searchable evidence repository. Also, preserve the rationale behind decisions. Why this field? Why this retention period? Why this transfer? That reasoning matters. The Act squarely places responsibility on the Data Fiduciary, and where consent is the basis, the business must be able to prove compliant notice and consent. If you cannot produce evidence quickly, your compliance story falls apart quickly too.

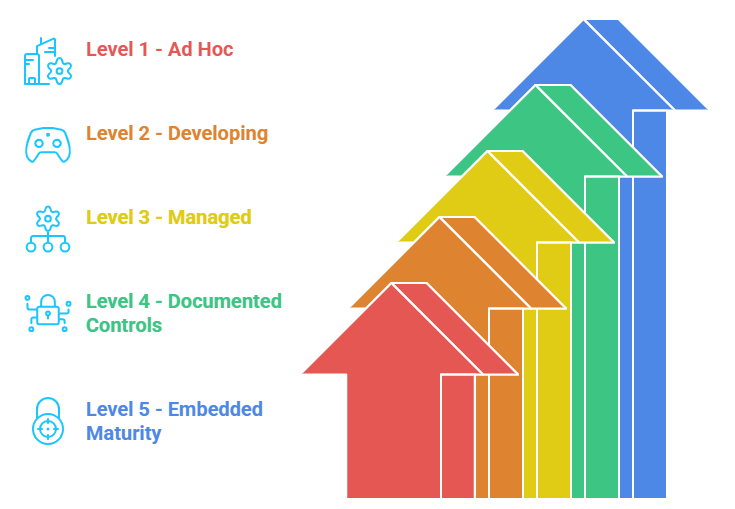
Compliance Maturity Levels
A simple maturity model helps teams stop arguing and start prioritising.
Level 1 is ad hoc: scattered notices, unclear ownership, weak evidence, and manual chaos.
Level 2 is developing: a few controls exist, but they do not connect.
Level 3 is managed: inventories, consent flows, rights handling, and vendor reviews exist, yet execution is still uneven across business units.
Level 4 is where most Indian businesses should aim before May 2027: controls are documented, tested, monitored, and tied to operations, not just legal theory.
Level 5 is embedded maturity, where privacy by design, algorithm due diligence, audit readiness, and executive oversight are routine. Score yourself honestly. If governance is weak, fix that first. If data mapping is broken, stop expanding the collection. If the evidence is thin, build the proof layer before anyone asks for it.
Conclusion
If governance is weak, fix that first. If data mapping is broken, stop expanding the collection. If the evidence is thin, build the proof layer before anyone asks for it.
That deadline will arrive faster than you think, so delay is risky. You need clean records, clear consent flows, and tighter daily controls. Small gaps today can turn into bigger legal and business problems tomorrow. A steady checklist helps you fix weak spots before pressure starts building. It also makes your teams faster, calmer, and far more consistent. You do not need drama, last-minute scrambling, or messy compliance guesswork. You need a practical path that keeps your business ready every day. For clear support before May 2027, you can trust Matayo.


